TOP 10 Asterisk Security Best Practices Results at 10Bestify.com
-
MSR Revo Ascent Snowshoe (2017 Model), 25-Inch
Our new rugged Revo Ascent snowshoes are engineered to take you anywhere you want-or need-to go. That confidence starts with their Extract deck, which combines external steel teeth for gripping the contours of any slope, with supreme durability and the torsional flex of plastic for excellent purchase. Steep terrain demands the security of our Posi Lock AT bindings and Ergo Televators heel lifts, while the snowshoe's reinforced nose withstands kick stepping on ascents through any conditions. Asterisk Security Best Practices
- ASIN: B00LFJO5NI
- UPC: 040818056165
- ASIN: B00LFJO5NI
- Brand: MSR
- Size: 25-Inch
- Manufacturer: MSR
-
Walnut Hollow Hotstamps Number and Symbol 24 Piece Set for Branding and Personalization on Wood and Leather
A set of Metal Stamps to brand and personalize many surfaces including paper, card, fabric, leather, wood, paper mache, gourds and nuts. This 24 piece set includes the following Numbers 0-9; Symbols - Asterisk, Pound, Exclamation, Question, Ampersand, Music Note, Ribbon, Star, Heart, "S" Brand, Comma, Circle, Square and Tree. Use the stamps to create a variety of fun patterns or to add dates to any project. The individual metal letters are designed to fit any of the Walnut Hollow Hot Tools which are available for purchase from Amazon (38283 Versa Tool, 5570 Value Woodburner, 24414 Detailer and 28094 Hobby Tool). Simply screw the stamps into the tool, allow to heat and add burn the design into your project. The stamps are approximately 5/8-inches (16mm) tall and the width will vary with eac... [Read More] Asterisk Security Best Practices
- ASIN: B0018NDH5S
- UPC: 046308273999
- ASIN: B0018NDH5S
- Brand: Walnut Hollow
- Manufacturer: Walnut Hollow
-
Thriving from A to Z : Best Practices to Increase Resilience, Satisfaction, and Success
Thriving from A to Z provides you with 26 best practices proven to help you learn, grow, and succeed. The essential best practices, valuable implementation tips, and engaging reflection activities help you build resilience and overcome challenges. The journal pages give you space to record your action steps. You'll use the tips and activities daily to create a life filled with more satisfaction and success both personally and professionally. The ability to thrive is not a given; it is an intentional choice. Choose to create your best self today.Thriving from A to Z delivers a straightforward pathway everyone can follow Asterisk Security Best Practices Thriving from A to Z provides you with 26 best practices proven to help you learn, grow, and succeed. The essential best practices, valuable implementation tips, and engaging reflection activities help you build resilience and overcome challenges. The journal pages give you space to record your action steps. You'll use the tips and activities daily to create a life filled with more satisfaction and success both personally and professionally. The ability to thrive is not a given; it is an intentional choice. Choose to create your best self today.Thriving from A to Z delivers a straightforward pathway everyone can follow
- UPC: 662577702
-
(isc)2 Cissp Certified Information Systems Security Professional Official Study Guide, 8e & Cissp Official (Isc)2 Practice Tests, 2e
This value-packed packed set for the serious CISSP certification candidate combines the bestselling (ISC)² CISSP Certified Information Systems Security Professional Official Study Guide, 8th Edition with an all new collection of Practice Exams to give you the best preparation ever for the high-stakes CISSP Exam. (ISC)² CISSP Study Guide, 8th Edition has been completely updated for the latest 2018 CISSP Body of Knowledge. This bestselling Sybex study guide covers 100% of all exam objectives. You'll prepare for the exam smarter and faster with Sybex thanks to expert content, real-world examples, advice on passing each section of the exam, access to Asterisk Security Best Practices This value-packed packed set for the serious CISSP certification candidate combines the bestselling (ISC)² CISSP Certified Information Systems Security Professional Official Study Guide, 8th Edition with an all new collection of Practice Exams to give you the best preparation ever for the high-stakes CISSP Exam.(ISC)² CISSP Study Guide, 8th Edition has been completely updated for the latest 2018 CISSP Body of Knowledge. This bestselling Sybex study guide covers 100% of all exam objectives. You'll prepare for the exam smarter and faster with Sybex thanks to expert content, real-world examples, advice on passing each section of the exam, access to the
- UPC: 326998267
-
Securities Industry Essentials Exam for Dummies with Online Practice
9781119545002 Asterisk Security Best Practices Get ready to qualify for the security industry job of your dreamsThe Securities Industry Essentials (SIE) Exam is a new test administered by FINRA beginning in October 2018. This exam is required as a prerequisite to each series level knowledge exam (such as Series 7). If you're prepping for the exam, you need a trusted resource to ensure your very best performance.Securities Industry Essentials Exam For Dummies with Online Practice gives you everything you need to score high on this important exam. With two practice tests in the book, plus two bonus tests online, you can practice your way to
- UPC: 581873790
-
Heroic Leadership : Best Practices from a 450-Year-Old Company That Changed the World
Shows how Jesuits have successfully grappled with the same challenges that test great companies today with an emphasis on their adopted values: self-awareness, ingenuity, love, and heroism. Asterisk Security Best Practices Leadership Principles for Lasting Success Leadership makes great companies, but few of us truly understand how to turn ourselves and others into great leaders. One company—the Jesuits—pioneered a unique formula for molding leaders and in the process built one of history’s most successful companies.In this groundbreaking book, Chris Lowney reveals the leadership principles that have guided the Jesuits for more than 450 years: self-awareness, ingenuity, love, and heroism. Lowney shows how these same principles can make each of us a dynamic leader in the twenty-first
- UPC: 3378981
- Rating: 4.5

-
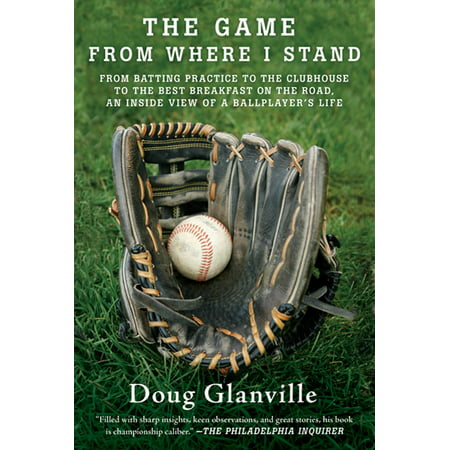
The Game from Where I Stand : From Batting Practice to the Clubhouse to the Best Breakfast on the Road, an Inside View of a Ballplayer's Life
Offers insight into the human aspect of professional baseball, including how players deal with family and teamwork issues, prepare for games, cope with slumps, and manage the competitive Asterisk Security Best Practices "Filled with sharp insights, keen observations, and great stories, his book is championship caliber." —The Philadelphia InquirerDoug Glanville, a former major league outfielder and Ivy League graduate, draws on his nine seasons in the big leagues to reveal the human side of baseball and of the men who play it.In The Game from Where I Stand, Glanville shows us how players prepare for games, deal with race and family issues, cope with streaks and slumps, respond to trades and injuries, and learn the joyful and painful lessons the game imparts. He also tells us with insight and humor what he
- UPC: 14902805
- Rating: 3.111

Asterisk Security: Common Mistakes and Prevention Methods
Astricon 2012 - Security Philip Mullis / PennyTel This presentation illustrates the multiple ways in which a system can be compromised and exploited by hackers, with examples! Asterisk specific com...
Asterisk Security Threats and Best Practices
Attacks on Asterisk-based telephony systems, which result in thousands of dollars' worth of stolen minutes, are not uncommon. Don't let this happen to you and your customers! Over 99% of the attack... Asterisk,threats,IP-PBX,VoIP,telephony attack,business telephone system,protect,Xorcom,telephony
Asterisk Security Webinar Part 1 of 4
Part 1 of the Asterisk VoIP Security Webinar. Special Agent Michael McAndrews reviews the current trends in VoIP fraud. Check out the other three parts for more information on securing your Aster... asterisk,security,voip,webinar
© 10Bestify.com - all rights reserved - Sitemap 10Bestify.com is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com